Is WPA2 no longer safe?
R
eported yesterday early morning, by Mathy Vanhoef a “KRACK”ing new discovery has been made in wi-fi security. However, don’t take the pun lightly, as this is a major vulnerability in a lot of wi-fi networks. Yes, we do mean a lot. This includes both personal and enterprise based wi-fi networks. However, the vulnerability isn’t a weak password or a public network scare like we’ve been informed many times before. This vulnerability is in the handshake of the connection itself.
Presently, the discoverer of the attack and other are unaware if this vulnerability is being used in the wild. So, for now, you might be ok. But, we will cover this in just a moment. So, let’s have a closer look at what Mathy has found and what this means for your wireless security. More importantly, what you can do about it.
If you are worried about your network’s security, then we are here to help. Feel free to give us a call on 01865 717088 . We offer full network security audits for free and will advise on your best options moving forward to improve it.
Never Miss a Post
Subscribe to our newsletter and we will let you know as soon as the next blog post is out.
Plus, get exclusive discounts and tips straight from the team at Computer Assistance.
So, what’s the Vulnerability?
The first thing we should discuss is what the vulnerability actually is. We briefly mentioned in the intro that it’s to do with the handshake in the connection between the device and the AP (Access point). But, what exactly is being exploited?
WPA2 (Wi-Fi Protected Access II) uses a 4-way handshake process with a device. This confirms that both the device and the AP are in possession of the correct credentials (the pre-shared password for the network). Furthermore, the 4-way handshake is responsible for negotiating an encrypted connection between the device and AP. All modern wi-fi networks use this, so potentially any of them are at risk from this. 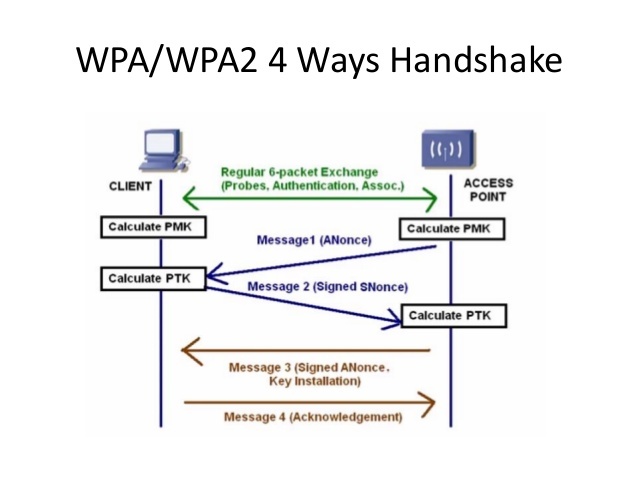
KRACK stands for Key Reinstallation Attacks. The process involves tricking the device/victim into re-installing an already-in-use encryption key. This is achieved by replaying the cryptographic handshake messages, during connection negotiation. We need to get a little more technical here. When the key is reinstalled, the incremental transmit packet number and receive packet number are reset to their initial values. Now, for security, a key should only be installed and used once. However, this is not a guarantee by the WPA2 protocol. Thus, this can be exploited.
In the 4-way handshake, the device will install the encryption key generated on the 3rd out of 4 messages. However, sometimes these messages may get lost or be dropped. Therefore, the AP will re-send the message if it doesn’t receive a message of acknowledgement. So, the device may re-install the same encryption key and, as a result, reset the incremental transmit packet number and receive packet number. KRACK exploits this drop, by replaying these retransmissions of message 3 of 4-way handshake. Thus, the protocol can be attacked by replaying packets, decrypting packets and maybe forging them.
Am I at risk?
Potentially, yes. Since all modern wi-fi networks use WPA2 protocol or similar, your device is at risk from being exploited during your connection to the Access Point.
However, let’s not immediately set all things electronic on fire and live in a shed in the middle of the woods. Let’s look at this logically and break down this vulnerability a little bit.
1. It’s not easy performing this exploit
Your average joe isn’t going to be able to pull off this attack. In fact, only those with a high skill set and actually know what they’re doing precisely will be able to pull this off. It’s not exactly an easy attack to perform. Furthermore, the details on how to actually perform and retransmit the resent message 3 in the 4-way handshake are not readily available online. There are no leaked instructions on how to perform this!
2. They need to be within your wi-fi signal’s range.
Let’s say the attacker knows how to perform the above attack and is ready to rumble. They will still need to be within signal range of your device and access point. No, this does not mean start setting up surveillance and large, metallic walls surrounding your business/home. The chance of someone going out of their way to access your device and snoop information off you in your own home is
less than the chance of being struck by lightning or winning the lottery. So, rest assured, your data is safe.
3. The IT industry aren’t slouches
This sort of vulnerability isn’t going to be left out there as a potential threat. In fact, Microsoft have already released a security update fixing this vulnerability. Furthermore, Google has stated that they will be rolling out a patch “in the coming weeks”. So, don’t panic.
4. Not every device is affected
Whilst it may be true that all if not most of modern wi-fi networks will be affected by this, the same cannot be said for the devices. The vulnerability mostly affected android devices. Although the windows and iOS devices were affected, the severity was not to the same degree. There was a group vulnerability present, but it did not have anywhere the same impact. The research paper conducted by Mathy Vanhoef focused around the android OS, since a lot of users don’t update their software. However, it’s also due to the vulnerability being expressed moreso on wpa_supplicant v2.4, commonly used on linux and android 6.0+.
What can I do?
If you are still concerned about your network security after reading this, the best options practices are as follows: 
-
- Keep your devices up to date. We cannot stress this enough. This is how individuals still get affects by already patched attacks. If you see an update pending for your android OS on your phone, we recommend doing it. It usually only takes a couple of minutes, but can save you a lot of hassle in the future.
- Temporarily stop broadcasting your SSID. Whilst this won’t necessarily help if the attacker already knows your network, it can be helpful to hide your SSID. The benefit is that your network isn’t constantly showing up as an available network. Thus, people searching for wi-fi networks to connect to won’t notice your network. However, we must stress this as a temporary measure, as it is more cumbersome to add someone you trust to your wireless network this way. So, we’d suggest turning off your SSID for a couple of weeks until android is patched, then turning it back on.
- Don’t panic. It’s not as bad as it sounds. I know this may sound a little silly to some, but don’t panic too much about this. If anything, this was more of an interesting discovery that was handled in an appropriate manner. Vendors and appropriate businesses were notified of this vulnerability months before it was publicly presented. So, rest assured that your devices are safe and you’re not suddenly going to have all your data stolen.
Useful links
If you want to read on a little more about KRACK, here are some useful links for you. Included will be a link to the original paper and documentation, as well as the main website and other news articles that covered this story, for further reading and developments.
The KRACK article main website
The KRACK paper
Microsoft already fixed this vulnerability
Until next time!
Still concerned about your wireless security? Why not get peace of mind with a full network security audit and consultation from the experts?
Feel free to give us a call on 01865 717088 and book a time that’s convenient for you for us to come around. We will then do a full network security audit of your building. From there, we will recommend the best practices and solutions moving forward to keep your important data safe.
While you’re at it, why not join our newsletter? We’ll send you a message when our next blogpost is up and ready for consuming. Furthermore, you’ll also receive some exclusive tips and information, as well as discounts on device repairs you book in with us! So, check the footer of this page, fill in your e-mail address and click Sign up. That’s all there is to it!
